If you are just starting out in cybersecurity, you have probably heard names like Nmap, Metasploit, or Wireshark thrown around. But nobody tells you what they actually do, where they fit, or which one you should even touch first.
This blog will give you a clear breakdown of the 10 most widely used ethical hacking tools in 2026, what each one does, why it exists, and what beginners consistently get wrong with it. Whether you are looking for the best hacking software for beginners or trying to understand how security professionals actually work, this blog gives you the full picture.
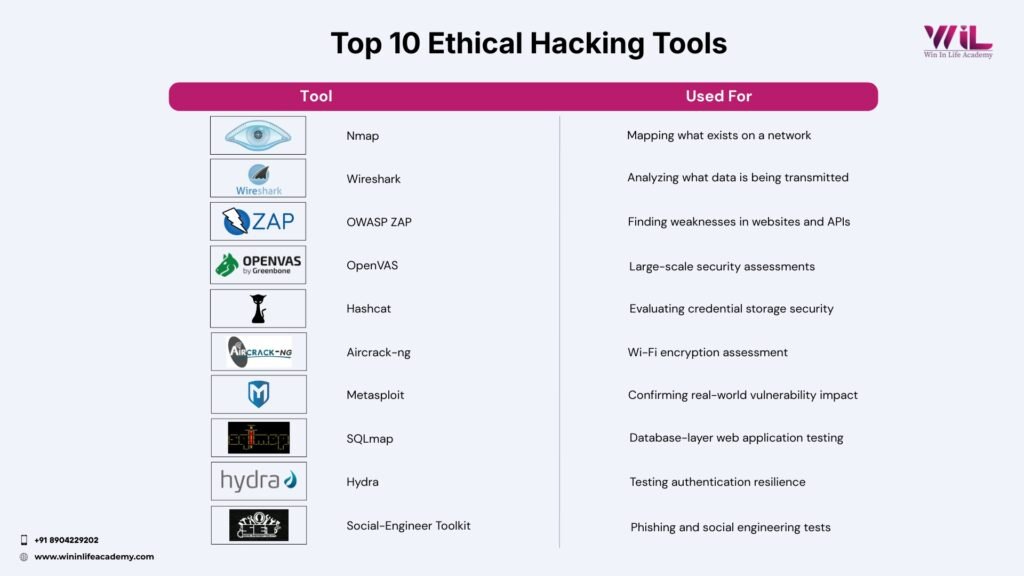
Top 10 Ethical Hacking Tools for Beginners

1. Nmap
Nmap is a network scanning tool that shows you what devices are connected to a network, what ports are open on those devices, and what services are running on those ports.
Think of it like a security guard doing rounds in a building. The guard checks every door, every window, every entry point to see which ones are unlocked and what is behind them. Nmap does exactly that for any network, digitally.
Before an ethical hacker tests anything, they need to know what they are even looking at. You cannot find weaknesses in something you cannot see. Nmap gives you that first clear picture of a target network. It shows you every device that is visible, every open door into those devices, and what software is sitting behind those doors. That information becomes the foundation for everything that follows in a security test.
Where most beginners go wrong is they run the scan, get a list of results, and have no idea what to do with it. Seeing “Port 22 open” means nothing if you do not know that Port 22 is used for remote access and that a poorly configured remote access service is one of the most common ways attackers get into systems. The scan output is not the answer. It is the starting point for asking better questions. If you want to get hands-on with Nmap commands immediately, this Nmap cheatsheet covers everything you need.
2. Metasploit
Metasploit is a penetration testing framework that lets ethical hackers test whether a known vulnerability in a system can actually be used by an attacker in the real world.
Think of it like a structural engineer who finds a crack in a building’s foundation. Writing it down in a report is one thing. Actually testing whether that crack would cause the building to collapse under pressure is another. Metasploit is the testing part.
Finding a vulnerability is not enough for an organization to act on it. Security teams need to know whether that vulnerability is actually dangerous or just a theoretical risk sitting in a low-traffic corner of the system. Metasploit answers that question by simulating what a real attacker would do, in a controlled and authorized environment, so the organization can understand the true severity of what has been found.
The mistake beginners make here is treating Metasploit like a shortcut. They search for an exploit, run it, and either declare a system compromised or safe based purely on whether the exploit executed. That tells you almost nothing useful.
Real usage requires understanding what vulnerability is being tested, why that vulnerability exists in the first place, and what the actual business impact would be if an attacker used it. Without that understanding, you are just pressing buttons. If you are trying to decide where Metasploit fits relative to other testing tools, this breakdown of Burp Suite vs Metasploit is worth reading.
3. Wireshark
Wireshark is a network protocol analyzer that captures all data traveling across a network in real time and lets you examine it in detail.
Imagine standing at a busy post office where you can open and read every letter passing through. You can see who sent it, who it is going to, and exactly what it says. Wireshark does that for data moving across a network. Every piece of information being transmitted between devices becomes visible and readable.
The reason this matters in security testing is that many systems send sensitive data across a network without properly protecting it. Login credentials, session tokens, personal information, internal communications. If that data is not encrypted, Wireshark will show it in plain text. Ethical hackers use this to prove to organizations that their data is exposed in transit, which is a risk most organizations do not realize they have until someone demonstrates it with a live capture.
Beginners consistently make the same mistake with Wireshark. They open it, see thousands of packets flooding the screen, and start clicking on individual ones trying to find something interesting. That approach gets you nowhere.
The real skill is learning to use filters to isolate specific types of traffic, specific protocols, or specific devices. Without filters, Wireshark is overwhelming noise. With filters, it becomes one of the most revealing tools in the entire ethical hacking toolkit. If you are new to it, start with what Wireshark is and how it works before jumping into live captures.
Not Sure Where to Start With All of This?
Most beginners who read lists like this one still cannot explain their way through a single tool in a job interview because knowing the name is not the same as knowing the workflow. Seven more tools to go, and without a structured path, they all start blurring together.
Win In Life Academy’s Cybersecurity Program gives you a structured path from zero to job-ready.
Explore Now4. OWASP ZAP
OWASP ZAP is a web application security testing tool that automatically scans websites and web applications to identify security vulnerabilities. It is an open-source project maintained by OWASP, one of the most trusted authorities in web application security globally.
Think of it as a building inspector who goes through an entire structure room by room, checking every wall, every outlet, every pipe for anything that violates safety standards. OWASP ZAP does that for websites, systematically checking every input field, every login form, every page and API endpoint for security weaknesses.
The reason this tool exists is that most modern applications live on the web. Your banking app, your company’s internal portal, the e-commerce site you use daily. All of them have input fields, login systems, and data flows that can be exploited if they are built incorrectly. OWASP ZAP helps ethical hackers find those weaknesses before real attackers do, across the entire surface of a web application, not just the obvious parts.
What beginners get wrong here is taking the automated scan report at face value. OWASP ZAP will flag potential vulnerabilities, but not every flag represents a real problem. Some are false positives.
A beginner will hand over a scan report as their final finding without verifying whether each item is actually exploitable. That is not security testing. That is running a tool and printing the output. Every finding in the report needs to be manually investigated before it can be called a confirmed vulnerability. For those moving from OWASP ZAP into more advanced web testing, how to implement Burp Suite is a natural next step.
5. SQLmap
SQLmap is an automated tool that tests whether a website’s database can be manipulated through its input fields using a technique called SQL injection.
When you type something into a search bar on a website, that input travels to a database which finds matching results and sends them back to you. SQL injection is what happens when instead of a normal search term, someone types a command that the database accidentally executes. SQLmap tests whether a website is vulnerable to that kind of manipulation.
This matters because databases are where everything valuable lives. Customer records, passwords, payment information, internal business data. A successful SQL injection attack can expose an entire database to an attacker without them needing to break through any other layer of security. SQLmap automates the process of identifying whether that door is open, which would take hours to do manually across a large application.
The critical mistake beginners make is running SQLmap without understanding SQL injection at all. If you do not understand how a database query works and why accepting unfiltered user input is dangerous, the tool output will mean nothing to you.
Learn basic SQL, understand what injection looks like when done manually, and then use SQLmap to scale what you already understand. Skipping straight to the tool means you will not know what to do with what it finds.
From Zero to Placed: Here is What Structured Learning Actually Looks Like
Yashwanth B A spent months going through tutorials and random tools with no direction, feeling like he was learning everything and understanding nothing.
He joined Win In Life Academy’s Cybersecurity Program , and four months later walked into his first role as a VAPT Analyst at Nexavise Consulting Pvt. Ltd.
The tools did not change. The structure did.
Explore Now6. Hashcat
Hashcat is a password cracking tool that tests how strong stored passwords are by attempting to reverse their hashed versions using high-speed computation.
When a website stores your password, it does not store the actual word. It stores a scrambled version called a hash. Hashcat works by generating billions of possible passwords, hashing each one, and comparing the result to the stored hash until it finds a match. Think of it as a locksmith who does not pick the lock but instead tries every key ever made at machine speed until one fits.
Organizations need to know whether the passwords their users have set would survive an attack if their database were ever stolen. According to the Verizon 2025 Data Breach Investigations Report, credential abuse accounts for 22% of all breaches, making it the single most common initial access method attackers use. Hashcat helps security teams understand exactly how long it would take to crack their stored credentials and whether their current password storage method provides real protection.
Beginners focus on the wrong thing here. They get excited about cracking speed and how many passwords they can crack per second. That completely misses the point. The actual lesson is understanding why certain hashing algorithms fail, what password salting does and why it matters, and how to advise an organization on storing credentials securely. The cracking is just a demonstration. The security design recommendation that follows is the real deliverable.
7. Aircrack-ng
Aircrack-ng is a wireless network security testing tool used to capture Wi-Fi traffic and evaluate how strong the encryption protecting that network actually is.
Your Wi-Fi network is essentially a conversation happening through the air. Aircrack-ng is like having a highly sensitive microphone that can capture that conversation and then test whether the scrambling protecting it is strong enough to keep it private. If the encryption is weak or misconfigured, the contents of that conversation become readable.
Wireless networks are one of the most overlooked attack surfaces in both home and enterprise environments. An attacker does not need to be inside a building to target a Wi-Fi network. They need to be within range. Aircrack-ng lets ethical hackers assess whether the wireless encryption in place, whether WPA2 or WPA3, is actually configured correctly and whether it would hold up against a real attack targeting that network from outside the building.
The common beginner mistake is ignoring the encryption standards entirely and just focusing on whether the tool produced a result. WPA2 and WPA3 are not the same thing. WEP, an older protocol, is completely broken and should never be in use. Understanding the difference between these standards and why some fail faster than others is the actual security knowledge this tool is designed to build. The result of the test is secondary to understanding why you got that result.
Still Wondering If This Is Actually Achievable for Someone Like You?
Manupriya M was six years into a non-technical career when she decided she wanted more. No networking background, no coding experience, no idea where to start.
She joined Win In Life Academy’s Cybersecurity Program and five months later was placed as a Junior Network Security Engineer at Indyanet Enterprise Network.
She did not get lucky. She just stopped learning randomly and started learning in the right order.
Next Batch Fit?8. Hydra
Hydra is a login testing tool that evaluates authentication systems by rapidly attempting large numbers of username and password combinations to determine whether the system can be broken through brute force.
Picture someone standing at a door with a machine that tries thousands of different key combinations per minute. Not picking the lock, just trying every possible key until one works. Hydra is that machine, applied to login pages, SSH services, FTP servers, and dozens of other authentication systems across different protocols.
The security question Hydra answers is straightforward. If an attacker simply tried every common password combination against this login system, would they eventually get in? And if so, how quickly? Many systems have no protection against this type of attack, meaning an attacker with patience and the right wordlist could walk through the front door without any sophisticated technique at all. Hydra tests whether that door is properly defended.
Where beginners go wrong is running Hydra without understanding the system they are testing first. Most production systems will lock an account or block an IP address after a certain number of failed login attempts.
A beginner who does not check for these protections first will either accidentally lock out real user accounts during an authorized test or waste significant time running an attack that the system is already blocking silently. Knowing the target’s behavior before running the tool is what separates a methodical test from a chaotic one.
9. OpenVAS
OpenVAS is a vulnerability scanning tool that runs thousands of security checks across a network or system simultaneously and produces a structured report of everything it finds, ranked by severity. Vulnerability severity in OpenVAS is scored using the CVSS (Common Vulnerability Scoring System) framework maintained by NIST, the industry standard for categorizing security risk.
Think of it as a full body health scan for an entire network. Instead of checking one thing at a time, OpenVAS runs thousands of diagnostic tests in parallel and hands you a report that says here is everything that needs attention, here is how serious each item is, and here is where you should start.
Here is the business reality behind why this tool matters: according to IBM’s Cost of a Data Breach Report, the global average cost of a single data breach is $4.44 million. That number exists largely because vulnerabilities go undetected for too long. OpenVAS is one of the primary tools organizations use to close that gap before an attacker finds it first.
In large organizations, there can be hundreds of servers, workstations, and network devices all running at the same time. Checking each one manually for known vulnerabilities, outdated software, and security misconfigurations is not a realistic task for any security team. OpenVAS makes that process systematic and scalable.
The mistake beginners make with OpenVAS is treating the report as a finished product. OpenVAS produces a long list of findings and beginners either get overwhelmed by the volume or assume everything on the list needs to be fixed with equal urgency. Real security work requires prioritization.
A critical vulnerability on a server that is directly accessible from the internet is not the same as a medium severity finding on an isolated internal test machine. Learning to read a vulnerability report and rank findings by actual business risk is the skill OpenVAS is designed to develop. Understanding the information security lifecycle gives you the broader framework that makes OpenVAS outputs actionable.
10. Social-Engineer Toolkit (SET)
The Social-Engineer Toolkit is a framework used to simulate attacks that target people rather than technology, including phishing emails, fake login pages, and credential harvesting scenarios.
Every other tool on this list finds weaknesses in systems. SET finds weaknesses in people. Think of it as a fire drill, except instead of testing whether people know where the exits are, you are testing whether they would hand their access badge to a stranger who knocked on the door wearing a convincing uniform.
The reason this tool exists is that human behavior is consistently the most exploited vulnerability in any organization. The Verizon 2026 Data Breach Investigations Report found that 68% of breaches involve a human element. That single stat is the entire argument for why SET exists.
An attacker does not need to break through a firewall if they can convince one employee to click a link and enter their credentials on a fake login page. SET helps ethical hackers simulate exactly those scenarios, measure how susceptible an organization’s people are to social engineering, and give the organization concrete data to build better security awareness training around.
Beginners almost always treat SET as a technical tool and completely miss the point. They focus on building convincing phishing pages and measuring click rates. The real lesson is understanding why people fall for these attacks, which cognitive biases attackers exploit such as urgency, authority, and familiarity, and how organizations can build a culture where employees recognize and report these attempts.
The human layer is the hardest vulnerability to patch. AI-generated phishing has made this significantly worse. Attackers now produce highly personalized, convincing messages at machine speed, which means defenders need to train people to question intent, not just spot bad grammar. Understanding common attack vectors in cybersecurity alongside SET gives you a complete picture of how human-layer attacks are structured. For a deeper look at how AI is being weaponized in this space, read GenAI security risks you need to know.
Which Ethical Hacking Tools Should You Learn First?
If you just finished reading all ten tools and feel more overwhelmed than when you started, that is not a sign this field is not for you. It is a sign you are missing a structured starting point. Here is where to begin based on where you are right now.
| Where You Are Right Now | Start Here | Then Move To |
| Complete beginner, no IT background | Learn networking basics first, then Nmap | OWASP ZAP |
| Basic networking knowledge | Nmap | OWASP ZAP, then Metasploit |
| Comfortable with Linux and networking | Nmap, then Metasploit | SQLmap, Wireshark |
Learning ethical hacking tools without a structured sequence is the single biggest reason beginners stall. Win In Life Academy’s Cybersecurity Program is built around exactly that sequence, from fundamentals to placement-ready.
Ready to become an Ethical Hacker?
You now know what the best ethical hacking tools are and how they fit together. The next question is whether you figure out the path forward alone or with a structure that has already placed students into real cybersecurity roles.
Yashwanth is now a VAPT Analyst. Manupriya is a Junior Network Security Engineer. Both started exactly where you are right now, with no clear direction and a browser full of open tabs. The difference was how they prepared for it.
Win In Life Academy’s Cybersecurity Program is where that structured path begins.
Start HereFrequently Asked Questions
1.What ethical hacking tools should a beginner learn first?
Start with Nmap. It requires no prior hacking knowledge, teaches you how to see a network the way an attacker does, and is referenced in almost every stage of real security testing. Once you are comfortable reading Nmap output, move to OWASP ZAP for web application basics. If you want a structured path that sequences all of this for you, the Win In Life Academy Cybersecurity Program is built exactly for that. Learn more here.
2. Is ethical hacking software free to use?
All ten tools covered in this guide are free and open source. The investment required is time spent understanding what each tool is showing you, not money spent on software licenses.
3. Are these ethical hacking tools legal to use?
The tools themselves are legal. What determines legality is how and where you use them. Using any of these tools against a system you do not own or have explicit written permission to test is illegal in most countries regardless of your intent. Always practice in a lab environment or with formal written authorization.
4. What skills do I need before using these ethical hacking tools?
At minimum you need a basic understanding of how networks work, comfort with Linux command-line navigation, and a basic understanding of how websites and web applications function. Without these foundations, you will use the tools without understanding what they are showing you. This guide on top cybersecurity analyst skills breaks down exactly what to build first.
5. Which of these tools is used most in real professional engagements?
Nmap, Metasploit, and OWASP ZAP consistently appear in professional penetration testing engagements. Nmap is almost always the starting point. The specific combination depends on the type of engagement, whether it is a network test, web application test, or a full red team assessment.
6. How long does it take to learn these ethical hacking tools?
Getting comfortable with the basics of each tool takes a few weeks per tool depending on how much time you put in daily. A structured program compresses that timeline significantly compared to self-learning. Win In Life Academy’s Cybersecurity Program is designed to take you from beginner to placement-ready in a matter of months, not years. Check the upcoming batch details here.
7. What is the safest way to practice using these tools as a beginner?
Use dedicated practice platforms like TryHackMe or Hack The Box, which provide legal, isolated environments designed for this purpose. Win In Life Academy’s Cybersecurity Program also includes guided lab environments where you practice legally and safely from day one. Find out more here.
8. Do I need certifications to use these tools professionally?
You do not need a certification to use the tools. You do need certifications to get hired in most professional roles. The most recognized ones are CompTIA Security+, CEH (Certified Ethical Hacker), and OSCP (Offensive Security Certified Professional). This cybersecurity certification guide for beginners walks you through which one to pursue based on where you are right now.
9. What cybersecurity roles use these tools professionally?
These tools are used daily by penetration testers, VAPT analysts, SOC analysts, and network security engineers. These are among the most in-demand roles in cybersecurity right now. For a detailed look at what those roles involve, read SOC analyst roles and responsibilities. For placement opportunities, see companies hiring cybersecurity freshers in India.
10. Can these tools be used for malicious purposes?
Yes, which is exactly why legal and ethical context matters. Every tool in this guide was built for legitimate security testing but can be misused. Ethical hacking is defined by authorization and intent, not by the tools themselves.





