AI in ethical hacking is transforming how security professionals work, not replacing them. It automates repetitive tasks like scanning and analysis while shifting the focus toward decision-making and strategy. To stay relevant, ethical hackers must understand how to use AI effectively within modern cybersecurity workflows.
AI in ethical hacking doesn’t mean your job is disappearing. It means the role has levelled up.
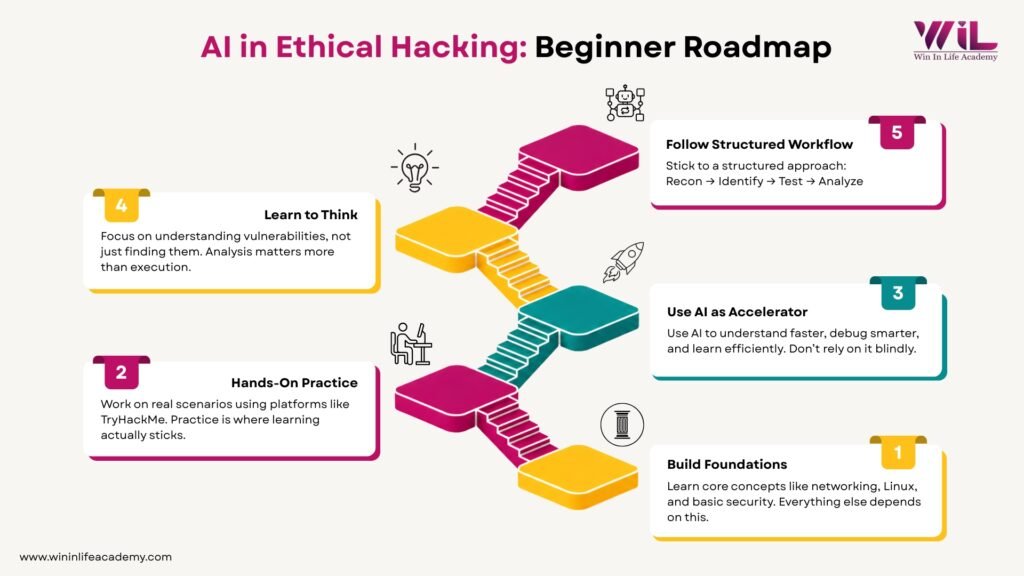
In 2026, if you’re planning to become an ethical hacker, being AI-enabled isn’t optional. But this isn’t about casually using AI tools or asking questions and copying answers. It’s about understanding where AI actually fits into your workflow, where it adds speed, and where human judgment still matters. That’s where the real advantage is in ethical hacking with AI.
This blog breaks it down in simple terms—how AI in ethical hacking is changing the field, where it’s actually used, how it’s applied in real scenarios, and the one question everyone keeps asking: does AI replace ethical hackers?
If you’re planning to learn ethical hacking or upgrade your skills, you need to understand this shift before you start.
Key Takeaways
- AI is reshaping ethical hacking by automating repetitive tasks and improving speed, but human judgment remains essential.
- The role of ethical hackers is evolving toward analysis, interpretation, and decision-making rather than just tool execution.
- Learning ethical hacking today requires understanding AI-driven workflows, not just traditional methods.
- Starting now with the right approach gives beginners an advantage as the cybersecurity landscape continues to evolve.
How AI is Changing Ethical Hacking
AI in ethical hacking is not a distant trend or something limited to research labs. It is already embedded into how modern security teams operate, and it is quietly changing the way work gets done at every stage of cybersecurity with AI.
Earlier, ethical hacking involved a lot of manual effort. Tasks like collecting information, scanning systems, analyzing logs, and testing vulnerabilities required time, patience, and a steep learning curve. That hasn’t disappeared, but a significant portion of that effort is now being handled by AI systems. The result is not less work, but a different kind of work where speed increases and expectations shift.
To understand this properly, it helps to look at how each part of the workflow has evolved.
1. Reconnaissance is Becoming Structured Instead of Manual
Reconnaissance used to be one of the slowest parts of the process because it required gathering scattered pieces of information from multiple sources and making sense of them manually. Ethical hackers had to identify domains, map IP ranges, check exposed services, and build a picture step by step.
Today, AI systems are capable of doing much of this groundwork automatically. Training bodies like EC-Council already highlight how machine learning models can scan environments, correlate data, and present a structured view of potential entry points. At the enterprise level, platforms developed by CrowdStrike go further by continuously mapping attack surfaces across networks and identifying risks in real time.
Instead of scattered manual effort, the process now looks like this:
- Automated scanning of domains, IPs, and exposed services
- Correlation of data from multiple sources into a single view
- Identification of high-risk entry points before manual analysis begins
What this changes is not just speed, but the starting point of the work itself. Instead of spending hours collecting information, professionals begin with a mapped environment and focus on interpreting what actually matters.
2. Vulnerability Detection is Shifting from Rules to Patterns
Traditional vulnerability detection relies heavily on known signatures, which means it is effective only against previously identified threats. This creates a gap when dealing with new or evolving attack techniques.
AI reduces that gap by focusing on patterns instead of fixed rules. Research from MIT, referenced by EC-Council, demonstrated that AI-driven systems could detect a large percentage of attacks while significantly reducing false positives.
In real-world environments, companies like Darktrace have shown how this works in practice. During incidents involving malware such as Gootloader, their AI systems were able to connect small, seemingly unrelated activities into a complete attack pattern before the threat fully executed.
This shift is important because detection is no longer limited to what tools already “know.” It now includes what they can infer—something that is becoming a core part of modern ethical hacking skills:
- Identifying unusual behavior instead of only known signatures
- Linking multiple low-level events into a single attack chain
- Reducing false positives so teams focus on real threats
3. Log Analysis is Moving from Data Overload to Decision Support
One of the biggest challenges in cybersecurity has always been the volume of data. Logs generated by systems, applications, and networks are far too large for manual analysis to be effective.
AI changes this by processing large datasets, identifying deviations from normal behavior, and surfacing only the most relevant signals. Organizations like IBM use AI-driven systems such as Watson to analyze logs and detect unusual patterns, including insider threats that might otherwise go unnoticed.
Similarly, Darktrace has demonstrated how AI can detect subtle command-and-control communication patterns hidden within normal network traffic.
In practical terms, this is where AI cybersecurity tools play a critical role by handling what humans cannot scale:
- Processing millions of log entries across systems
- Detecting anomalies based on behavior, not just rules
- Highlighting only high-risk signals instead of raw data
As a result, the role of a security professional shifts from scanning raw data to interpreting filtered insights and making informed decisions.
Online Certifications
Build practical cybersecurity skills to protect systems, networks, and data in real-world environments. Learn how cyber attacks occur, how organizations defend against them, and how security professionals secure digital infrastructure, aligned with globally recognized certifications.

Duration: 6 months
Learn at your own pace
Skills you’ll build:
Understanding Cyber Attacks and Defense Mechanisms
Security Operations and Incident Handling
Vulnerability Assessment and Ethical Hacking Basics
Firewall, IDS/IPS, and Network Protection Concepts
Practical Security Tools and Lab Practice
Certification-Aligned Cybersecurity Knowledge
Real-World Security Practices and Career Readiness
4. Exploit Development and Testing is Becoming Assisted
For beginners, exploit development has traditionally been one of the most difficult stages because it requires both programming knowledge and a deep understanding of system behavior.
AI is reducing that friction by assisting with code generation, explanation, and debugging. Even large technology companies like Google are using AI internally for automated red teaming, where systems simulate attacks and test defenses in controlled environments.
This assistance typically shows up in three ways:
- Generating scripts or payload structures to get started faster
- Explaining existing code so you understand what it is doing
- Helping debug errors and refine testing approaches
However, this does not eliminate the need for understanding. AI can support the process, but it cannot replace the need to know why something works or fails.
5. Security is Becoming Continuous Instead of Periodic
The traditional approach to ethical hacking often involved periodic assessments. Systems were tested at specific intervals, reports were generated, and the process repeated later.
Modern environments no longer operate that way. AI-driven systems enable continuous monitoring, where behavior is tracked in real time and anomalies are detected as they occur. Companies like CrowdStrike have built platforms that continuously monitor endpoints, prioritize threats, and respond quickly within Security Operations Centers.
This shift changes the entire operating model:
- Monitoring happens continuously, not at fixed intervals
- Threats are detected as they emerge, not after damage is done
- Response time is significantly reduced through automation
For professionals entering the field, this evolution is shaping the future of cybersecurity and the overall ethical hacking career path.
6. Prioritization is Improving Through Context, Not Just Alerts
A long-standing problem in cybersecurity has been the overwhelming number of alerts generated by security systems. Many of these alerts are low-risk or false positives, which makes it difficult to identify what truly requires attention.
AI addresses this by adding context and prioritizing threats based on behavior and impact. Reports from organizations like IBM show how AI is being used to analyze attack patterns, rank risks, and reduce the overall noise in security operations.
Instead of reacting to everything, systems now help teams focus:
- Ranking alerts based on severity and potential impact
- Reducing false positives that waste time
- Providing context so decisions are clearer and faster
7. The Role of the Ethical Hacker is Evolving
The most important change is not in the tools, but in the role itself.
Earlier, ethical hackers were expected to execute tasks manually from start to finish. Today, their role increasingly involves selecting the right tools, interpreting AI-generated outputs, validating results, and making decisions based on context.
This shift can be understood clearly:
- From executing tasks → to supervising and interpreting systems
- From manual effort → to strategic decision-making
- From tool usage → to workflow understanding
Even the most advanced AI systems cannot understand business priorities, organizational risk, or the intent behind an attack. Those aspects still require human judgment.
Why 2026 is the Right Time to Start in Ethical Hacking
If you’re considering getting into ethical hacking, timing actually matters. Right now, the industry is going through a shift, and that shift is creating a real advantage for beginners who start with the right approach.
Here’s why:
1. The Skills Shortage is Structural, Not Temporary
Organizations like (ISC)² continue to report millions of unfilled cybersecurity roles globally. This isn’t a short-term hiring gap. Companies simply don’t have enough skilled people, and demand keeps growing faster than supply.
2. AI Has Reduced the Early Learning Friction
A lot of the repetitive work that used to slow beginners down—basic scanning, scripting, log filtering—is now AI-assisted. You still need to learn the fundamentals, but you can start working on real problems much earlier than before.
3. The Definition of “Skill” Has Changed
Companies are no longer impressed by someone who can just run tools. They want people who can understand outputs, connect the dots, and make decisions. Most learners are still preparing the old way, which gives you an edge if you adapt early.
4. Attackers Are Already Using AI
AI is not just helping defenders. It’s being used to automate phishing, generate exploits, and scale attacks faster than ever. That increases the demand for professionals who understand AI-driven threats, not just traditional techniques.
5. The Industry is Still Figuring Itself Out
This isn’t a stable, settled field right now. Experienced professionals are adapting, companies are experimenting, and training systems are catching up. That makes entry easier because no one has fully mastered this shift yet.
6. New Roles Are Emerging with No Legacy Competition
Areas like AI red teaming, adversarial testing, and model security didn’t exist a few years ago. There are no “10-year veterans” dominating these roles yet, which creates a rare opening if you start early.
7. Certifications and Training Are Updating Right Now
Organizations like EC-Council and CompTIA are actively updating their frameworks to include AI-driven security. Starting now means you learn the current standard instead of unlearning outdated practices later.
AI vs Ethical Hackers: Will You Be Replaced?
This is the question most people don’t say out loud, but it’s always there in the background.
If AI can scan systems, detect threats, analyze logs, and even generate code, then what exactly is left for a human to do?
The short answer is simple: AI is changing the role, not removing it.
What AI Can Actually Do Well
AI is extremely good at handling scale, speed, and repetition. It can process data faster than any human and spot patterns across systems that would take hours or days to identify manually.
In practical terms, AI is already being used to:
- Scan large environments and identify potential vulnerabilities
- Analyze massive volumes of logs and flag anomalies
- Assist in writing and debugging scripts
- Detect patterns across multiple stages of an attack
This is why companies are investing heavily in AI-driven security systems. It makes the entire process faster and more efficient.
Where AI Still Falls Short
What AI cannot do is understand context the way a human does.
It does not understand:
- Business impact of a vulnerability
- Why a system is designed a certain way
- The intent behind an attacker’s actions
- Trade-offs between risk, cost, and usability
For example, an AI system might flag a vulnerability as “critical” based on technical severity. But only a human can decide whether that vulnerability actually matters in a real business environment.
The Real Relationship: Not Replacement, But Leverage
The idea of “AI vs Ethical Hackers” is misleading. It’s not a competition.
The real shift is this:
- AI handles the repetitive, data-heavy work
- Humans handle interpretation, strategy, and decision-making
A good ethical hacker today is not someone who does everything manually. It’s someone who knows how to use AI to move faster while still understanding what’s happening underneath.
This is the difference between:
- Someone who runs tools
- And someone who actually understands security
Who Actually Gets Replaced
This is where most people get uncomfortable, but it needs to be said clearly.
AI will not replace ethical hackers.
But it will replace people who:
- Only follow step-by-step instructions
- Don’t understand what their tools are doing
- Rely on outputs without questioning them
At the same time, someone who knows how to use AI properly will outperform someone who doesn’t.
So, the real competition is not AI vs human. It’s human with AI vs human without AI.
Conclusion
AI is no longer an add-on in ethical hacking. It has already changed how the work is done, what skills matter, and how quickly someone can become useful in the field. The shift is clear: less focus on repetitive execution, more focus on understanding systems, interpreting outputs, and making decisions. For anyone exploring ethical hacking for beginners, this is actually an advantage if approached correctly.
That’s where choosing the right starting path matters. Instead of following outdated methods, it makes more sense to learn within a system that already reflects current practices. Programs like Cybersecurity Course from Win In Life Academy are designed with this shift in mind and help you build real, job-relevant skills aligned with the modern ethical hacking career path.
If you’re planning to step into this field, the goal is simple: start with the right approach and build momentum early.
FAQs
1. What is AI in ethical hacking in simple terms?
AI in ethical hacking means using smart tools to automatically find, analyze, and prioritize security issues instead of doing everything manually.
2. How is AI used in cybersecurity and ethical hacking?
AI is used for tasks like automated scanning, threat detection, log analysis, and identifying unusual behavior across systems to prevent attacks faster.
3. Can AI replace ethical hackers in the future?
No, AI cannot fully replace ethical hackers because it lacks human judgment, context understanding, and decision-making ability. It acts as a tool, not a replacement.
4. Is ethical hacking a good career option in India in 2026?
Yes. With increasing cyber threats and a shortage of skilled professionals, ethical hacking continues to be a high-demand and growing career in India.
5. What skills are required for AI-based ethical hacking?
You need a mix of fundamentals like networking and Linux, along with the ability to use AI tools, interpret outputs, and understand security workflows.
6. Do I need coding skills to learn ethical hacking with AI?
Basic coding helps, but it’s not mandatory to start. AI tools can assist with writing and understanding code, but you still need to understand the logic behind it.
7. What are the best AI tools used in ethical hacking?
Common AI-driven tools include automated vulnerability scanners, anomaly detection systems, and AI-assisted scripting tools used in modern security operations.
8. How can beginners start learning ethical hacking in 2026?
Start with fundamentals, practice on platforms like TryHackMe and Hack The Box, and use AI tools to speed up learning and understanding.
9. What is the future scope of AI in cybersecurity?
AI will continue to play a major role in detecting threats, automating security tasks, and improving response time, making it an essential part of cybersecurity careers.
10. Which certification is best for AI-based ethical hacking?
Certifications like CEH v13 AI are designed to align with modern cybersecurity practices and include AI-driven concepts.





