At first glance, information security and data security look like two names for the same thing. Both aim to protect information, both appear in cybersecurity discussions, and both are used in security frameworks. But inside real organizations, these terms describe different layers of protection and guide different security decisions.
In this article, we will unpack the difference between information security vs data security step by step. We will define both concepts, compare their scope and objectives, examine how organizations apply them in practice, and explore how each area connects to real cybersecurity roles and protection strategies.
What Is Information Security?
Information security is the broad practice of protecting information wherever it exists and in whatever form it takes. The aim is to keep sensitive material safe whether it is digital, printed, or verbally shared. This discipline is guided by three core priorities: confidentiality, integrity, and availability.
Confidentiality ensures only authorized people can access information. Integrity protects accuracy and completeness. Availability ensures access is possible when required.
Since information lives in many environments, protection involves more than technology. Policies, physical controls, access management, monitoring, and human responsibility all play important roles. Grasping this larger view builds the foundation needed to understand how security responsibilities are organized in real workplaces.
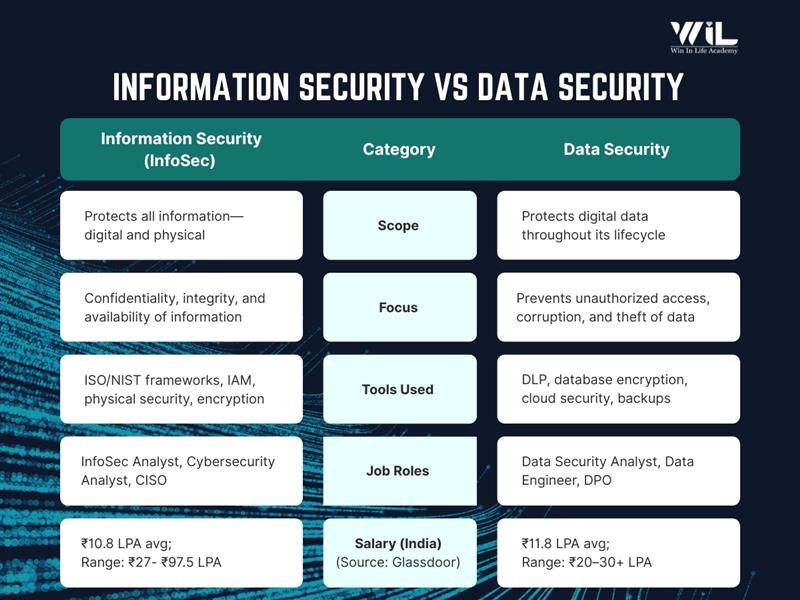
| Aspect | Information Security | Data Security |
|---|---|---|
| Scope | Protects all information environments | Protects digital data |
| Focus | Systems, users, infrastructure | Databases, files, records |
| Goal | Maintain confidentiality, integrity, availability | Prevent data exposure or theft |
| Controls | Policies, monitoring, access management | Encryption, masking, DLP |
| Roles | Security analyst, SOC analyst, GRC | Data security engineer, privacy engineer |
What Is Data Security?
Data security concentrates specifically on protecting digital data. The focus is on safeguarding files, records, and datasets that are stored, processed, or transmitted through computer systems. This area relies heavily on technical controls. Encryption, access restrictions, masking, backup protection, and secure transfer mechanisms are common ways organizations prevent exposure, misuse, or loss.
Because the scope is tighter, the work becomes more specialized. Professionals pay close attention to where data resides, who can reach it, how it moves between systems, and what could compromise it. Understanding this narrower focus helps clarify how security responsibilities are structured and why certain roles and tools are designed specifically around protecting digital assets.
Information Security vs Data Security
Both areas contribute to protecting an organization, but they operate at different levels and handle different types of responsibilities. To understand how they function in practice, it helps to examine them across multiple dimensions such as scope, objectives, methods of protection, ownership, and daily decision making.
Looking at these layers side by side reveals how strategy connects with implementation and how various security roles align within the larger framework. The comparisons below break this structure into clear, practical views.
1. Core Meaning
Information security represents the broad effort to keep all forms of information safe across an organization. It looks at the environment in which information exists, including technology, infrastructure, policies, and human interaction.
Data security concentrates on the protection of actual digital content. The attention is on preventing exposure, misuse, or loss of data while it is stored or moving between systems.
| Aspect | Information Security | Data Security |
|---|---|---|
| Simple Meaning | Protecting all information everywhere in an organization | Protecting the data itself |
| Easy Explanation | Protects the entire environment where information exists | Protects the actual data stored or transmitted |
| Example | Securing office systems, networks, and access | Encrypting a database |
2. Scope of Responsibility
Information security spans the full organizational landscape. It includes governance, infrastructure, user behavior, physical safeguards, and digital environments. Data security works within that larger landscape but stays focused on datasets, repositories, and data movement.
| Aspect | Information Security | Data Security |
|---|---|---|
| Scope | Very broad | Narrower |
| What Is Included | Systems, networks, people, policies, physical files, digital information | Databases, files, backups, data transfers |
| Coverage Level | Organization-wide | Data-level only |
| Relationship | Parent discipline | Part of information security |
3.Goals and Objectives
Information security aims to keep operations trustworthy and stable by ensuring confidentiality, integrity, and availability across the organization. Data security aims to make sure valuable digital assets cannot be accessed, altered, or stolen by unauthorized parties.
| Aspect | Information Security | Data Security |
|---|---|---|
| Primary Goal | Ensure confidentiality, integrity, and availability of information | Prevent data leaks, loss, or unauthorized access |
| Main Concern | Overall information safety | Data protection |
| Success Means | Information is secure across systems and processes | Data cannot be stolen or altered easily |
4.Protection in Action
Information security relies on governance structures, access frameworks, monitoring practices, and preparedness for incidents. Data security relies more heavily on technical enforcement mechanisms that directly shield datasets.
| Aspect | Information Security | Data Security |
|---|---|---|
| Type of Controls | Policies, access rules, monitoring, training, network security | Encryption, masking, backup, data access control |
| Focus Area | Managing risks and access across organization | Protecting stored and moving data |
| Examples | Security policies, identity management, incident response | Database encryption, DLP tools, file permissions |
5.Threat Ownership
Information security evaluates threats that could disrupt systems, misuse privileges, or harm the enterprise at large. Data security concentrates on dangers that specifically target the exposure or corruption of digital assets.
| Aspect | Information Security | Data Security |
|---|---|---|
| Threat Types | Cyberattacks, insider misuse, phishing, physical theft | Data breaches, leaks, corruption, accidental deletion |
| Who Handles It | Security teams, risk teams, governance teams | Security engineers, DB admins, data teams |
| Failure Example | Unauthorized system access allowed | Sensitive data exposed without encryption |
6.Industry Roles and Hiring
Organizations rarely recruit someone with a generic title. They hire specialists whose duties align either with broader protection strategy or with direct technical safeguarding of data. Information security positions often blend oversight with operations, while data security roles are typically deeper in implementation.
| Aspect | Information Security Roles | Data Security Roles |
|---|---|---|
| Typical Job Titles | Information Security Analyst, Security Engineer, SOC Analyst, GRC Analyst, Security Architect, Cybersecurity Analyst | Data Security Engineer, Database Security Engineer, Cloud Data Security Engineer, Privacy Engineer |
| Primary Responsibility | Protect systems, networks, access, and overall information environment | Protect sensitive data and prevent data exposure |
| Daily Work Focus | Monitoring threats, managing access, risk assessment, incident response, policy enforcement | Encryption setup, data access control, data classification, securing databases and storage |
| Tools Commonly Used | SIEM tools, IAM systems, firewalls, endpoint protection, vulnerability scanners | Encryption tools, DLP solutions, database monitoring tools, data masking tools |
| Decision Level | Often strategic plus operational | Mostly technical and implementation-focused |
| Example Task | Investigating suspicious login activity | Ensuring customer data is encrypted at rest and in transit |
7.Decision Perspective
The difference becomes extremely visible in the questions teams raise. Their priorities guide how they investigate risk and make decisions. Information security teams think about system trust and exposure. Data security teams think about what happens to the data inside those systems.
| Situation | Information Security Questions | Data Security Questions |
|---|---|---|
| New System Deployment | Who can access this system? How is authentication handled? What risks does this introduce? | What data will be stored? Is it encrypted? Who can read or export it? |
| Security Incident | How did the attacker enter? Which systems were affected? How do we stop it again? | What data was accessed or leaked? Was sensitive data exposed? |
| Access Management | Should this user have access at all? Is least privilege followed? | Does this user need access to this specific data? |
| Cloud Migration | Is the cloud environment securely configured? | Is data protected during transfer and storage? |
| Compliance Check | Are security policies followed? Are controls documented? | Is personal or sensitive data properly protected? |
Training Program
Build practical, job-ready skills to protect networks, systems, and digital assets from modern cyber threats. Learn how attackers operate, how defenses are built, and how organizations monitor and respond to risks.

Duration: 6 months
Learn at your own pace
Skills you’ll build:
Other Courses
Is Data Security Part of Information Security?
Yes. Data security sits within the wider discipline of information security.
Information security is responsible for safeguarding information in every form. That includes digital records, physical documents, communication channels, infrastructure, and the people who interact with them. It sets governance models, defines access principles, and ensures that protection supports business continuity.
Data security operates inside this framework with a tighter mission. It concentrates specifically on shielding digital data through mechanisms such as encryption, masking, permission control, and monitoring of how information is stored or transmitted.
Thinking of it as layers makes the relationship easier to grasp. The broader layer creates the environment of trust and control, while the inner layer ensures the actual digital asset remains protected within that environment. Understanding this hierarchy helps learners recognize how specialized roles contribute to a larger security strategy.
Why Organizations Use Both Information Security and Data Security
Modern enterprises protect far more than files. They must secure infrastructure, users, devices, applications, and information moving between them. Relying on a single approach would leave gaps, because risks appear at multiple layers.
Information security provides the structure. It defines policies, assigns accountability, manages access models, and prepares the organization to prevent, detect, and respond to threats that could disrupt operations.
Data security adds precision inside that structure. It ensures sensitive records remain unreadable to unauthorized parties, limits who can retrieve or modify them, and tracks how they travel across systems, clouds, and backups.
Using both allows companies to defend the environment and the assets within it. One builds the protective framework; the other reinforces the valuables that framework is meant to guard.
Information Security vs Data Security Example
Information Security: Consider a company where employees use internal applications to manage customer operations.
Before anyone even touches the data, several safeguards are already active. Staff must enter the facility using access cards. Systems require authentication and may demand multi-factor verification. Permissions are mapped to job roles, and monitoring teams watch for suspicious behavior such as unusual login times or access attempts.
The goal here is to protect the environment where information resides. If the environment is controlled, the opportunity for misuse becomes smaller.
Data Security: Now imagine an authorized employee successfully logs in.
Protection does not stop there. The database storing customer details may be encrypted. Sensitive identifiers might appear masked on the screen. Download or export privileges could be limited. Copies stored in backups remain protected, and transfers between systems are secured.
Here the mission is to defend the data itself, even when someone has legitimate access to the surrounding systems.
Where You Will See Information Security and Data Security in Cybersecurity Careers
When exploring career paths, the distinction becomes visible in how responsibilities are grouped and how employers define roles. Opportunities connected with information security usually span broad protection of systems, users, and operational stability.
Professionals in this space may work on governance, threat monitoring, identity models, audits, or enterprise architecture. The work often involves coordination across departments and balancing risk with business continuity.
Data security careers appear when organizations need specialists who can directly safeguard sensitive digital assets. These roles dive deeper into repositories, storage systems, and data flows.
Daily responsibilities frequently include encryption strategies, database protection, classification, masking, and preventing unauthorized extraction of information.
Recognizing where each area appears in hiring helps learners decide whether they prefer wide oversight across environments or concentrated technical defense around data itself.
Conclusion:
Information security and data security move toward the same goal: protecting what matters. The difference lies in the layer of responsibility. One establishes and governs a trusted environment through policies, access models, monitoring, and readiness. The other applies to technical safeguards that keep digital assets from being exposed, altered, or lost.
Understanding this structure helps aspiring professionals read job descriptions accurately, recognize where their interests fit, and choose learning paths that match industry expectations.
If you are preparing to build a future in cybersecurity, structured guidance and practical exposure make the journey clearer and faster. Win In Life Academy offers focused programs in Cybersecurity courses designed to help learners develop both foundational understanding and hands-on capability aligned with real workplace demands.
FAQ
1. What is the main difference between information security and data security?
Information security protects the overall environment that handles information, including infrastructure, users, and processes. Data security focuses specifically on defending digital content from unauthorized access or misuse. The distinction is mainly about breadth versus specialization.
2. Is data security a part of information security?
Yes, it functions within the broader protection framework established by organizations. While enterprise security creates safe operating conditions, data protection concentrates on the information stored and transmitted inside those systems. It represents a focused layer of defense.
3. Which is more important, information security or data security?
Both are critical for maintaining trust and continuity. If infrastructure fails, operations stop, and if information is exposed, reputational and legal damage can follow. Effective programs invest in both areas together.
4. Can you have information security without data security?
Not in a meaningful way. Strong control of networks and users will not help if sensitive datasets remain open to extraction or abuse. Attackers often look for exactly that imbalance.
5. Who is responsible for information security in a company?
Responsibility is usually shared across leadership, IT, risk teams, and employees. Policies, monitoring, and response require coordination rather than ownership by a single department. Security becomes part of organizational culture.
6. Who handles data security?
Specialized professionals typically manage these duties. Their work involves protecting storage locations, governing permissions, and ensuring safe movement of digital assets. The role is often deeply technical.
7. What tools are commonly used for data protection?
Organizations rely on encryption, activity monitoring, masking, and access restriction technologies. These solutions help reduce the chance of unauthorized viewing or copying. They also support regulatory expectations.
8. Does cybersecurity include both information and data security?
Yes, cybersecurity is the wider discipline that covers multiple protective layers. It includes defending infrastructure as well as the information those systems contain. Different specialists may focus on different parts.
9. Why do companies separate these functions?
Dividing responsibilities allows teams to build deeper expertise. Some focus on governance and operational risk, while others concentrate on safeguarding critical assets. This separation improves clarity and accountability.
10. Which skills should beginners focus on first?
Many professionals begin with fundamentals such as networking, authentication methods, and basic risk concepts. Understanding how environments function makes advanced protection techniques easier to learn. This path aligns well with hiring expectations.





